How to do Spy Pen Camera Data Recovery? Resolved Query

If you are looking forward for Spy Pen Camera Data Recovery, then you are on the right page. Spy pens are widely used for discreet recording and capturing important moments. It is a small yet powerful device which relies on memory cards to store your recorded data efficiently. This device can easily record several media files, such as photos, videos, and audio.
However, like any other storage device, these memory cards are very common for data loss. It can be due to accidental deletion, corruption, formatting or even any kind of physical damage. And if it is about the Spy pen camera, it can be very distressing, especially when the data is very important and crucial. In this situation you need to Recover Deleted Files from Spy Pen Camera Memory Cards very carefully so that no data of yours is lost.
In this article we are going to talk about how to restore deleted files from memory cards easily without even losing a single data file. Here you will explore several methods that will efficiently help you to retrieve deleted files from sd card efficiently. You just have to understand the steps of these methods carefully and you can easily complete this task as per your convenience.
Are you looking for a solution for Spy Pen camera data recovery? If yes then, no need to take any stress. Because of the booming upgrade in technology, the use of hidden spy pen cameras is increasing day by day. Sometimes users lost their crucial data such as videos, audio, and photos from spy gadgets pen cameras. After that, users try to find out a professional solution for solving these queries.
- How to retrieve deleted videos and audios from spy pen?
- How to recover lost data from spy pen camera SD Cards?
Reasons for Spy Pen Camera Data Recovery
There are several reasons to restore deleted files from sd card:
- You may delete your files unknowingly or accidentally during the operation or transferring your data.
- Unintended formatting of the Memory Card/ SD Card can also erase or corrupt all the data stored in.
- Memory card corruption takes place due to the improper handling or the malware as well. You need to be careful.
- You may not be able to access your files as damaged memory cards also make their files inaccessible.
- Very sudden interruptions during the transfer of your files can also make them inaccessible.
>Let us talk about the several methods that can be used to restore deleted files from memory cards to complete this procedure. There are some manual methods and there is a professional method as well. You need to understand the functioning of all those methods for the better results.
Method 1: Spy Pen Camera Data Recovery from the Recycle Bin
If you have transferred or deleted files from your spy pen camera while accessing it on the PC. you can check base folders and file or else recycle bin might be containing your deleted files. Below are the steps to restore it:
- First click on the recycle bin icon to open it. It must be on your desktop.
- Now just have to right-click on your file then select restore from the option and your file will be restored back to its original file.
Drawbacks of this Method
- This method only works if your files were deleted after transferring to a PC.
- Files deleted directly from your memory card will not appear in the recycle bin.
- It may take time finding your files to restore if they are in bulk.
Method 2: Restore from the Backup for Spy Pen Camera Data Recovery
It is good to backup your spy pen camera data on a regular basis. You might recover your data from the backup. Below are the steps to restore files from the backup:
- First of all, locate your file or folder on your external storage or cloud storage.
- Once you get the file from the storage, restore those required files to the memory card or your computer.
- Once restored you can easily use it in the best way you can.
Drawbacks of this Method
- With this method, if you already have a backup of your data file then only backup can be done easily.
- Old backups will contain old data, they will not include the most recent data.
Forensic Overview of Spy Gadgets
Today, underneath most of the objects we use, there lies the internal component of a spy device. Ranging from simple Spy Pen to Spy Bluetooth Glasses, the Spy Gadget market has a lot to empower our spying eyes. People use Spy gadgets for the purpose of keeping their valuables safe, computer spying, tracking locations, and video surveillance of covert operations, etc. where evidence gathering is of much importance. Spy gadgets allow you to spy on others by capturing or tracking photos, sounds, and whereabouts.
Some of the popular Spy gadgets are Spy Pen, Spy watch, Button Camera, pinhole size CMOS camera, Bluetooth Spy, Lighter Spy, PI Camstick, etc. For stalkers, there are pretty many options of SPY gadgets available. With the arrival of SPY gadgets and other surveillance gadgets, the privacy of individuals has gone for a toss. These gadgets come in disguise as a never though object from your daily life – So beware! As we mentioned there are Digital Spy devices available in different forms and types, most of the time they are used as hidden cameras. Serving the duty of a secret agent, these Spy devices are often stored house of valuable evidence and details of high forensic value. Anytime, anywhere, anyone is under threat of being spied.
Thus, the number of cases reported against Spying is also increased. In such a scenario, a call for applications that can recover data safely from spy Gadgets also arises. Here we are discussing the type of Spy gadgets, their technical overview, and options to recover data from different forms of Spy Gadgets.
Also Read: How Can I Recover Deleted Data from My Laptop?
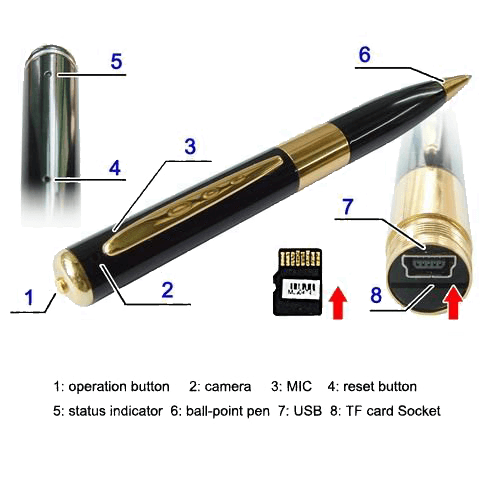
Secret Spy Pen Camera Technical Specification
According to the general principle followed, to assure interoperability, the file systems for sound and image files stored in a removable or non-removable memory should be FAT12, FAT16, or FAT32. Spy pen camera usually comes with 2 GB or more media capacity, thus the file system of the USB storage will be FAT16 or FAT32. The image output from any Spy gadget pen camera varies, depending upon the technical specification they use. Video Resolution, Image Resolution, Lux rating, Image Sensor Type, store type, store consumption type, frame rate, etc. derives the quality of evidence created by any hidden spy camera.
Playing James Bond is now everyone’s hobby with the perfect spy mini camera available with them. Reports say that there are secret spy pen camera gadgets specially designed to go undetected which can capture evidence successfully in form of images, videos, and sound files. As the use of spy pen cameras is everyone’s cup of tea now, the risk of data loss also increases.
General Scenarios of Data Loss from Spy Pen Camera SD Cards
- Perform accidental formatting of the Spy digital camera memory. It generally happens when the user unintentionally chooses the Format option as a result of Format Error within the device.
- Actions performed against infected files by the ANTIVIRUS in the system. It can also happen that virus-infected media files from the Spy device may be erased by the ANTIVIRUS scanning performed by the system to which it is connected.
- A virus or malware attack is a very threating scenario resulting in data corruption of Spy devices
- Selecting Delete All option while managing the files on Spy digital camera can result in removal of the entire recording from the memory card.
When this is the scenario faced by a general user, the one who performs Spy Pen Camera device investigation also has certain threats to overcome in artifact carving from Spy gadgets. As mentioned, there are Digital Spy devices available in different forms and types, most of the time they are used as hidden cameras. Serving the duty of a secret agent, these Spy devices are often stored houses of valuable evidence and details of high forensic value.
Critical Situations Faced by Forensics Investigators
- The Spy pen camera devices captured is showing inaccessibility error while connected with the system.
- Spy devices are shown as USB drive letters, but no trace of recordings are available.
- All the important files and recordings from the spy device are deliberately wiped out.
In the category of Spy camera, there are devices like car key chain camera, Mini Spy DVR Camera, Spy Glasses Camera with Hidden HD Camera, HD Pen Camera, Socket Camera, and many others. Due to the simple working format and complicated architecture, there is high rate of data loss possibilities while capturing the details of content within the Spy device.
Method 3: Spy Pen Camera Data Recovery Forensic Point of View
Forensics investigators give utmost importance to preserving the EXIF details of images and videos captured using the Spy device. In case of any error happenings also, the solution that guarantees the complete recovery of spy device recording without alteration is the first and last preference of any examiner. To present the data extracted from any Spy device in court it should be unaltered, accurate, and precise. In case of data corruption or data inaccessibility issues from the Spy device memory then the BitRecover Data Recovery software is the best choice. It’s a handy software that gives complete freedom for the investigator to retrieve the lost or corrupted data from Spy devices.
Manual efforts to recover deleted or lost images, videos or any form of media files from the Spy devices may result in data disaster. Thus, to avoid the risk, investigators’ choice is spy Device Data Recovery tool. When the corruption scenarios make the photo restoration from Spy devices difficult, then this tool can be a rescuer. This device supports the recovery of Spy device data connected and recognized as USB drive letter but fails to show any recordings. The tool performs smartly with the Windows OS including Win 11 and lower versions.
How to Recover Lost Data from Spy Pen SD Cards?
- Connect the spy pen camera to your computer.
- Run Spy pen camera data recovery tool on pc.
- Choose the recovery mode option as per your choice.
- Get spy camera memory card drive information.
- View the file to be recovered in the software panel.
- Select the required files and browse the destination path.
- Press Save to start retrieving the spy pen deleted data.
Uses Cluster by Cluster Forensics Grade Algorithms
Understanding the need to retain the EXIF information of the data from the spy device, the tool uses cluster-by-cluster forensics-grade algorithms to recover the evidence.
Some Tips to Avoid DATA Loss from Spy Cameras
- When taking photos, movies, or audio, always make sure the device’s battery is completely charged.
- Once you identify any kind of error in the image store, do not store new images or try to click more.
- Get a backup of the captured images in the external hard drive or in safety systems.
- If an error notice appears while attempting to view the file’s content, stop right there to avoid further data loss.
Spy Pen Data Recovery Solution FAQs
Q 1: My Spy Pen camera is recognized as a driver letter, but it is not showing any data. Can your software help?
A: Yes, if the Spy Pen is recognized as a drive letter in computer. After that software will be able to recover files from it.
Q: When I try to plug my spy pen drive, it prompts me with a message to format my device. What should I do?
A: The error message you are getting is due to a corrupt file system in your spy pen device. It seems you have removed your Spy Pen from your computer’s USB port without properly ejecting it. In your case software can recover your data from Spy Pen device.
Q: Does your software supports Spy devices using USB 3.0?
A: Yes, the software supports all USB devices, USB 1.0, 2.0, 3.0, etc.
Ending Lines
Now anyone can get this solution for spy pen camera data recovery and recover deleted data from all brand spy cameras such as HP, Sony, and all. The software has multiple recovery modes to retrieve lost data having multiple senecios.